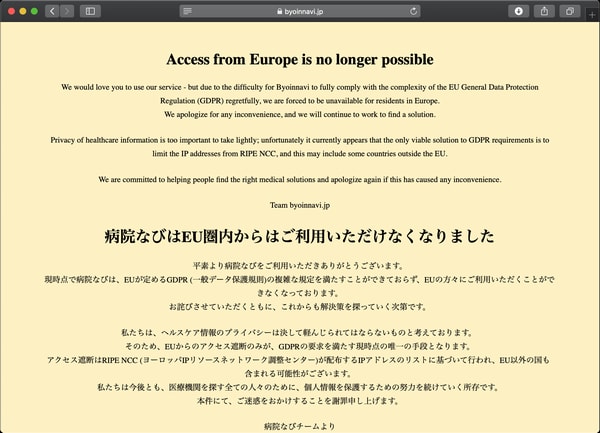
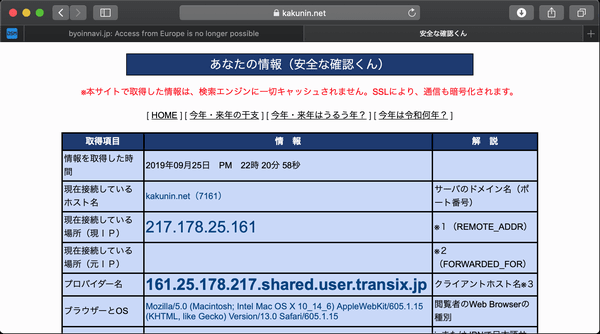
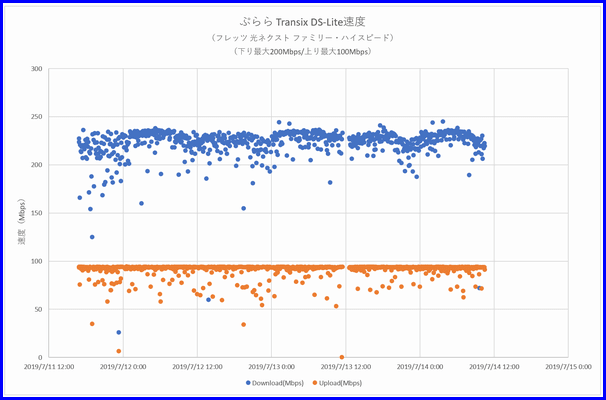
ぷららのTransix DS-Lite(IPv4 over IPv6)からのアクセスがヨーロッパ圏からのアクセス?
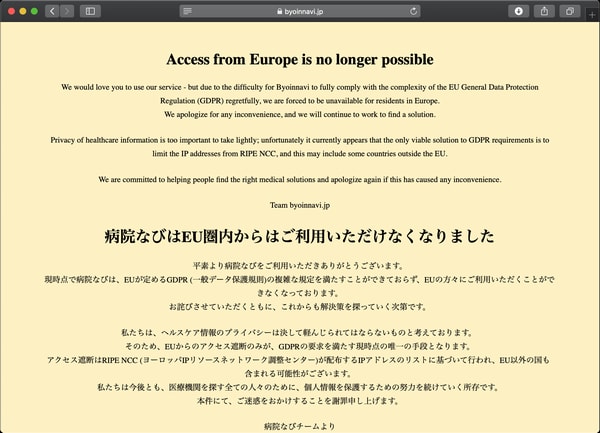
transix DS-Liteは、日本国内にあるかと。。。
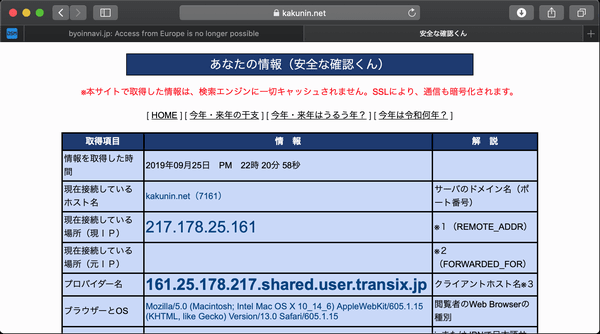
IPアドレスで判断する愚。。。。
また、ぷららのサポートに問い合わせるのかな。。。。。
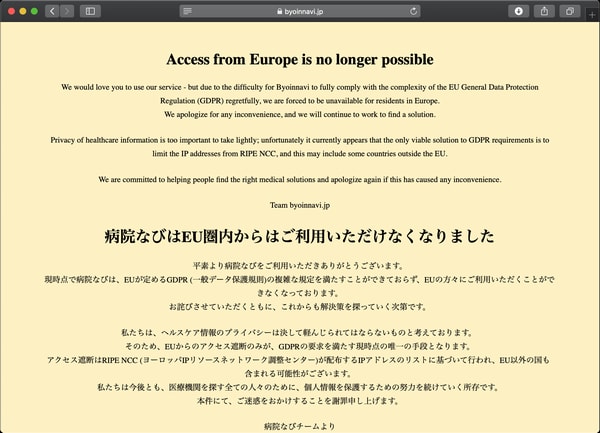
transix DS-Liteは、日本国内にあるかと。。。
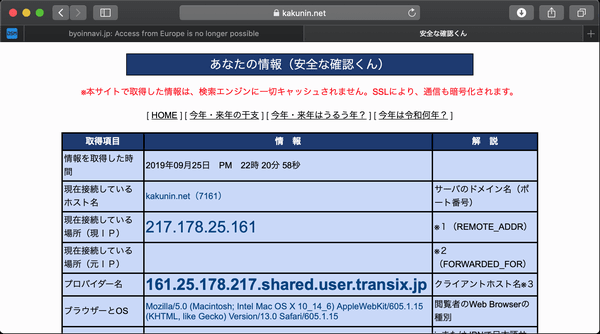
IPアドレスで判断する愚。。。。
また、ぷららのサポートに問い合わせるのかな。。。。。

AES-128-CBC
<key>ChildSecurityAssociationParameters</key>
<dict>
<key>DiffieHellmanGroup</key>
<integer>14</integer>
<key>EncryptionAlgorithm</key>
<string>AES-128</string>
<key>IntegrityAlgorithm</key>
<string>SHA1-96</string>
<key>LifeTimeInMinutes</key>
<integer>1440</integer>
</dict>
AES-256-CBC
<key>ChildSecurityAssociationParameters</key>
<dict>
<key>DiffieHellmanGroup</key>
<integer>14</integer>
<key>EncryptionAlgorithm</key>
<string>AES-256</string>
<key>IntegrityAlgorithm</key>
<string>SHA2-256</string>
<key>LifeTimeInMinutes</key>
<integer>1440</integer>
</dict>
AES-128-GCM
<key>ChildSecurityAssociationParameters</key>
<dict>
<key>DiffieHellmanGroup</key>
<integer>14</integer>
<key>EncryptionAlgorithm</key>
<string>AES-128-GCM</string>
<key>IntegrityAlgorithm</key>
<string>SHA1-96</string>
<key>LifeTimeInMinutes</key>
<integer>1440</integer>
</dict>
AES-256-GCM
<key>ChildSecurityAssociationParameters</key>
<dict>
<key>DiffieHellmanGroup</key>
<integer>14</integer>
<key>EncryptionAlgorithm</key>
<string>AES-256-GCM</string>
<key>IntegrityAlgorithm</key>
<string>SHA2-256</string>
<key>LifeTimeInMinutes</key>
<integer>1440</integer>
</dict>
/etc/ipsec.conf
conn %default
keyexchange=ikev2
#for Windows10 IKEv2 VPN
ike=aes256-sha256-modp1024
#for GCM testing
esp=aes128gcm16-sha, aes256gcm16-sha256
auto=add
left=%any
leftauth=pubkey
leftsubnet=192.168.0.0/20,2409:10:XXXX:YY00::/56,2404:1a8::/32
#for iOS VPN apli
leftsendcert=always
leftcert=debian10-pub.pem
leftid=@vpn.AAAAAAAA.mydns.jp
right=%any
rightsourceip=192.168.15.0/24,2409:10:XXXX:YY30::15:0/120
rightdns=192.168.11.250,2409:10:XXXX:YY20::11:250root@debian10:~$ lscpu
Architecture: x86_64
CPU op-mode(s): 32-bit, 64-bit
Byte Order: Little Endian
Address sizes: 36 bits physical, 48 bits virtual
CPU(s): 8
On-line CPU(s) list: 0-7
Thread(s) per core: 2
Core(s) per socket: 4
Socket(s): 1
NUMA node(s): 1
Vendor ID: GenuineIntel
CPU family: 6
Model: 42
Model name: Intel(R) Core(TM) i7-2600 CPU @ 3.40GHz
Stepping: 7
CPU MHz: 1596.243
CPU max MHz: 3800.0000
CPU min MHz: 1600.0000
BogoMIPS: 6784.69
Virtualization: VT-x
L1d cache: 32K
L1i cache: 32K
L2 cache: 256K
L3 cache: 8192K
NUMA node0 CPU(s): 0-7
Flags: fpu vme de pse tsc msr pae mce cx8 apic sep mtrr pge mca cmov pat pse36 clflush dts acpi mmx fxsr sse sse2 ss ht tm pbe syscall nx rdtscp lm constant_tsc arch_perfmon pebs bts rep_good nopl xtopology nonstop_tsc cpuid aperfmperf pni pclmulqdq dtes64 monitor ds_cpl vmx smx est tm2 ssse3 cx16 xtpr pdcm pcid sse4_1 sse4_2 x2apic popcnt tsc_deadline_timer aes xsave avx lahf_lm epb pti tpr_shadow vnmi flexpriority ept vpid xsaveopt dtherm ida arat pln pts
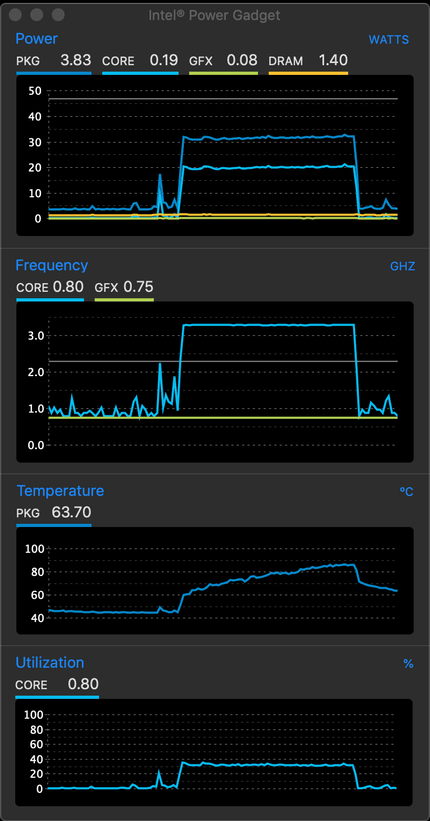
openssl speed aes-256-cbc
OpenSSL 1.1.1c 28 May 2019
built on: Thu May 30 15:27:48 2019 UTC
The 'numbers' are in 1000s of bytes per second processed.
type 16 bytes 64 bytes 256 bytes 1024 bytes 8192 bytes 16384 bytes
aes-256 cbc 84293.98k 89436.65k 90589.10k 91029.16k 91187.88k 91247.96k
openssl speed -evp aes-256-cbc
The 'numbers' are in 1000s of bytes per second processed.
type 16 bytes 64 bytes 256 bytes 1024 bytes 8192 bytes 16384 bytes
aes-256-cbc 393369.35k 491012.78k 523522.90k 532274.52k 534899.37k 535183.36k












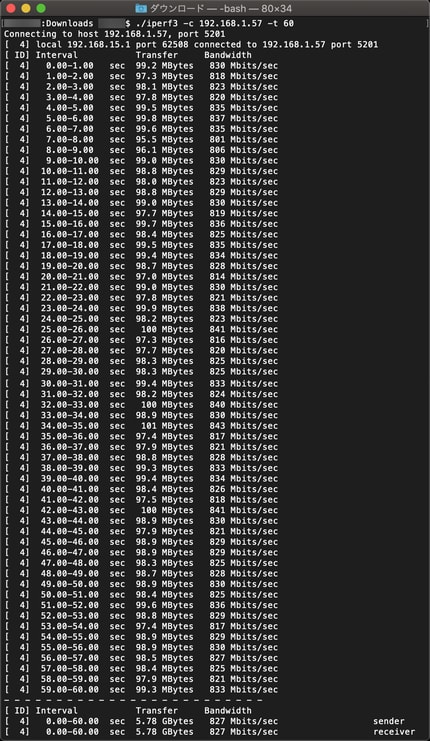
AES128-CBC 825Mbps AES256-CBC 682Mbps AES128GCM16 878Mbps AES256GCM16 824Mbps


/etc/ipsec.conf
config setup
# strictcrlpolicy=yes
# uniqueids = no
# charondebug="cfg 2,ike 2,esp 2"
conn %default
keyexchange=ikev2
#for Windows10 IKEv2 VPN
ike=aes256-sha256-modp1024
# esp=aes128-sha!
auto=add
left=%any
leftauth=pubkey
leftsubnet=192.168.0.0/20,2409:10:XXXX:YY00::/56,2404:1a8::/32
#for iOS VPN apli
leftsendcert=always
leftcert=debian10-pub.pem
leftid=@vpn.AAAAAAAA.mydns.jp
right=%any
rightsourceip=192.168.15.0/24,2409:10:XXXX:YY30::15:0/120
rightdns=192.168.11.250,2409:10:XXXX:YY10::11:250
conn eap-id-passwd
rightauth=eap-mschapv2
eap_identity=%any/etc/ipse.secrets
: RSA debian10-key.pem "key password"
user1 : EAP "user password"
/etc/strongswan.conf
charon {
load_modular = yes
plugins {
include strongswan.d/charon/*.conf
#for iOS/OSX IKEv2 VPN apli
attr {
25 = familyname,flets-east.jp
}
}
}
include strongswan.d/*.conf








/bin/python /volume1/homes/admin/speedtest-cli --list | /bin/grep "OPEN Project" | /bin/sed -E "s/([:digit:]*)\).*$/\1/g" | /bin/xargs -I % /bin/python /volume1/homes/admin/speedtest-cli --server % --csv >> /volume1/homes/admin/speedtest.csv
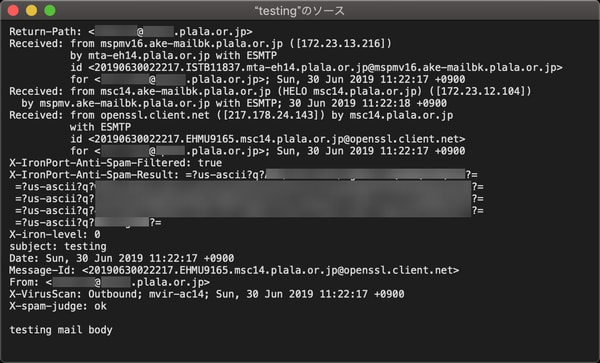
printf "%s\0%s\0%s" someone@any.plala.or.jp someone@any.plala.or.jp PASSWORD | base64 | tr -d '\n' | pbcopyecho -e "auth plain c29tZW9uZUBhbnkucGxhbGEub3IuanAAc29tZW9uZUBhbnkucGxhbGEub3IuanAAUEFTU1dPUkQ=\nquit" | openssl s_client -quiet -crlf -connect secure.plala.or.jp:465 2> /dev/null
220 msc11.plala.or.jp ESMTP server ready Mon, 17 Jun 2019 17:25:49 +0900
235 Authentication successful
221 msc11.plala.or.jp ESMTP server closing connectionecho -e "ehlo\nquit" | openssl s_client -connect secure.plala.or.jp:465 -quiet -crlf 2>/dev/null
220 msc12.plala.or.jp ESMTP server ready Sun, 23 Jun 2019 11:29:10 +0900
250-msc12.plala.or.jp
250-AUTH=LOGIN PLAIN CRAM-MD5
250-AUTH LOGIN PLAIN CRAM-MD5
250-PIPELINING
250-DSN
250-8BITMIME
250 SIZE 20971520
221 msc12.plala.or.jp ESMTP server closing connection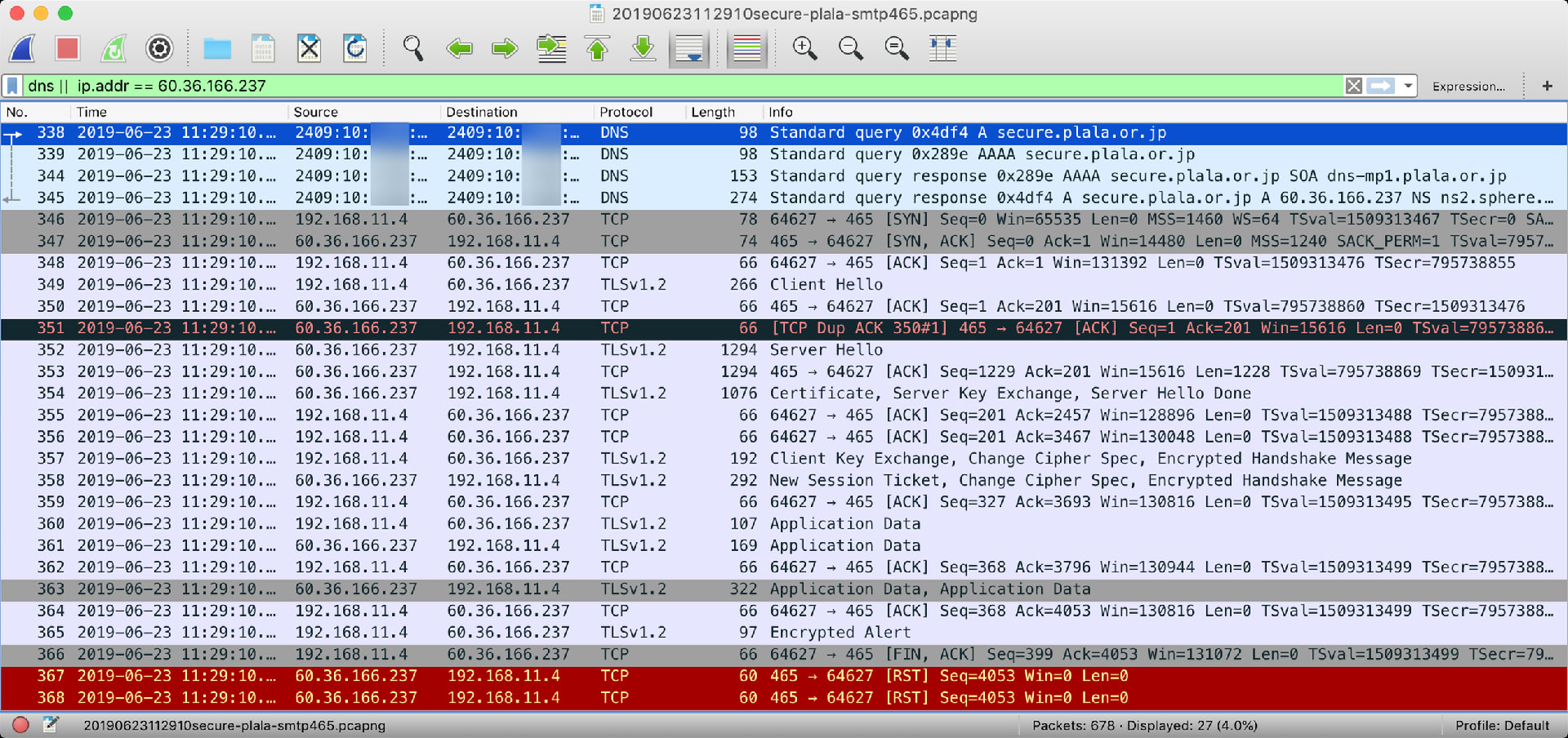
echo -e "ehlo\nquit" | openssl s_client -connect secure.plala.or.jp:465 -quiet -crlf -msg 2>/dev/null > smtp.log
cat smtp.log | grep -A 3 -e "ClientHello" | sed '1d' | tr '\n' ' ' | sed 's/ //g' | sed -e 's/^.\{12\}\(.\{64\}\).*$/\1/g'9420cdb22e9988f8a1e95918182a60d646622553e337e15d1fdcb4d991d91d7e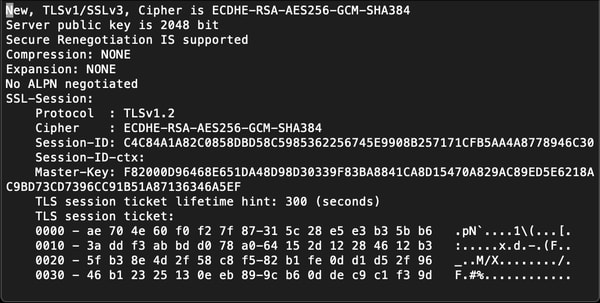 「Master-Key」を取り出す。
「Master-Key」を取り出す。cat smtp.log | grep -e "Master-Key:" | sed -e 's/^.*Master-Key: \(.*\)$/\1/g'F82000D96468E651DA48D98D30339F83BA8841CA8D15470A829AC89ED5E6218AC9BD73CD7396CC91B51A87136346A5EFcat smtp.log | grep -e "Session-ID:" | sed -e 's/^.*Session-ID: \(.*\)$/\1/g'C4C84A1A82C0858DBD58C5985362256745E9908B257171CFB5AA4A8778946C30--- pick-ssl-keys.sh ---
#!/bin/bash
fl1="smtp.log"
okf1="smtp-random-key.log"
okf2="smtp-session-key.log"
krand=`cat $fl1 | grep -A 3 -e "ClientHello" | sed '1d' | tr '\n' ' ' | sed 's/ //g' | sed -e 's/^.\{12\}\(.\{64\}\).*$/\1/g'`
ksess=`cat $fl1 | grep -e "Master-Key:" | sed -e 's/^.*Master-Key: \(.*\)$/\1/g'`
isess=`cat $fl1 | grep -e "Session-ID:" | sed -e 's/^.*Session-ID: \(.*\)$/\1/g'`
echo "CLIENT_RANDOM $krand $ksess" > $okf1
echo "RSA Session-ID:$isess Master-Key:$ksess" > $okf2
echo "CLIENT_RANDOM $krand $ksess"
echo "RSA Session-ID:$isess Master-Key:$ksess"CLIENT_RANDOM 9420cdb22e9988f8a1e95918182a60d646622553e337e15d1fdcb4d991d91d7e F82000D96468E651DA48D98D30339F83BA8841CA8D15470A829AC89ED5E6218AC9BD73CD7396CC91B51A87136346A5EF
RSA Session-ID:C4C84A1A82C0858DBD58C5985362256745E9908B257171CFB5AA4A8778946C30 Master-Key:F82000D96468E651DA48D98D30339F83BA8841CA8D15470A829AC89ED5E6218AC9BD73CD7396CC91B51A87136346A5EF$ ls smtp-*.logsmtp-random-key.log smtp-session-key.logcat smtp.log | awk '/Master-Key:/{key=$2} {b=1;e=16;if(l==3)b=7;if(l==1)e=6;for(i=b;i<=e;i++)s=s$i;if(l--==1)r[s]=1}/ ClientHello$/{l=3;s=""} END{for(rnd in r)print "CLIENT_RANDOM",rnd,key}'CLIENT_RANDOM 9420cdb22e9988f8a1e95918182a60d646622553e337e15d1fdcb4d991d91d7e F82000D96468E651DA48D98D30339F83BA8841CA8D15470A829AC89ED5E6218AC9BD73CD7396CC91B51A87136346A5EF
echo -e "auth plain c29tZW9uZUBhbnkucGxhbGEub3IuanAAc29tZW9uZUBhbnkucGxhbGEub3IuanAAUEFTU1dPUkQ=\nmail from: someone@any.plala.or.jp\nrcpt to: xxxxxxxx@yyyyy.plala.or.jp\ndata\nsubject: testing\ntesting mail body\n.\nquit" | openssl s_client -quiet -crlf -connect secure.plala.or.jp:587 -starttls smtp -msg 2>/dev/null > smtp.log$./pick-ssl-keys.sh